Attack Hardware: What It Is and Why You Should Care
Introduction:
In the world of cybersecurity, it’s important to be aware of the various threats that can compromise your systems. One such threat is attack hardware. Attack hardware refers to any physical device that is used to gain unauthorized access to a computer system or network. These devices can be as simple as a USB drive or as complex as a custom-built device designed specifically for an attack. In this blog post, I’ll explore what attack hardware is, how it works, and why you should care about it.

How Attack Hardware Works:
Attack hardware works by exploiting vulnerabilities in computer systems or networks. These vulnerabilities can be anything from a weak password to an unpatched software vulnerability. Attackers use these vulnerabilities to gain access to a system, and then use attack hardware to maintain that access or to escalate their privileges.
One example of attack hardware is a USB Rubber Ducky. This device looks like a regular USB drive, but it’s actually a tool for launching automated keystroke attacks. When plugged into a computer, the USB Rubber Ducky can execute a pre-programmed sequence of keystrokes to perform actions like opening a command prompt, downloading and executing malware, or exfiltrating data.
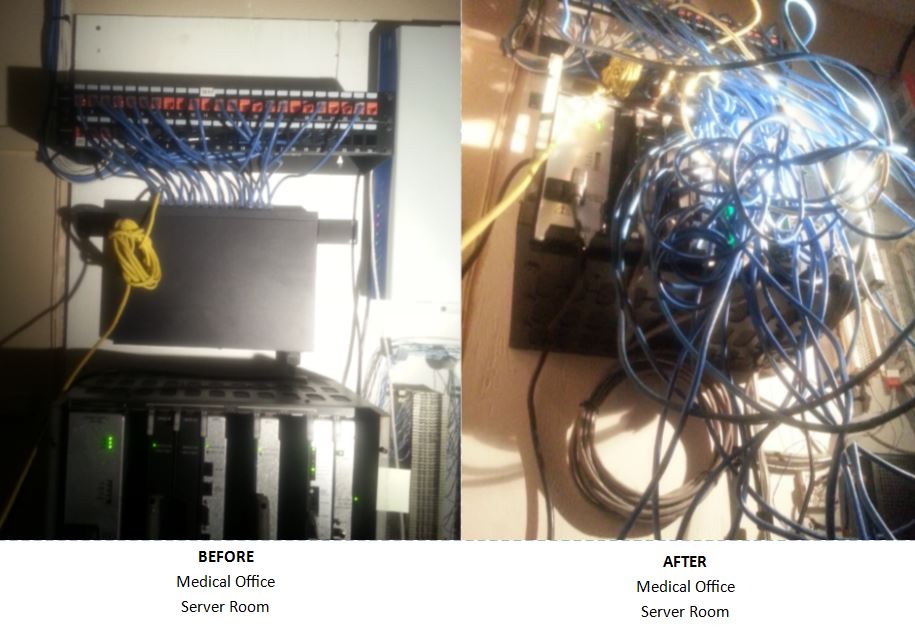
Another example of attack hardware is a network tap. This device is used to intercept network traffic between two devices. Attackers can use a network tap to capture sensitive data like passwords and other credentials, or to inject malicious traffic into the network.
Why You Should Care About Attack Hardware:
Attack hardware is a serious threat to computer systems and networks. It can be used to bypass security controls like firewalls and antivirus software and can give attackers persistent access to a system. Attackers can use this access to steal sensitive data, launch additional attacks, or disrupt critical systems.
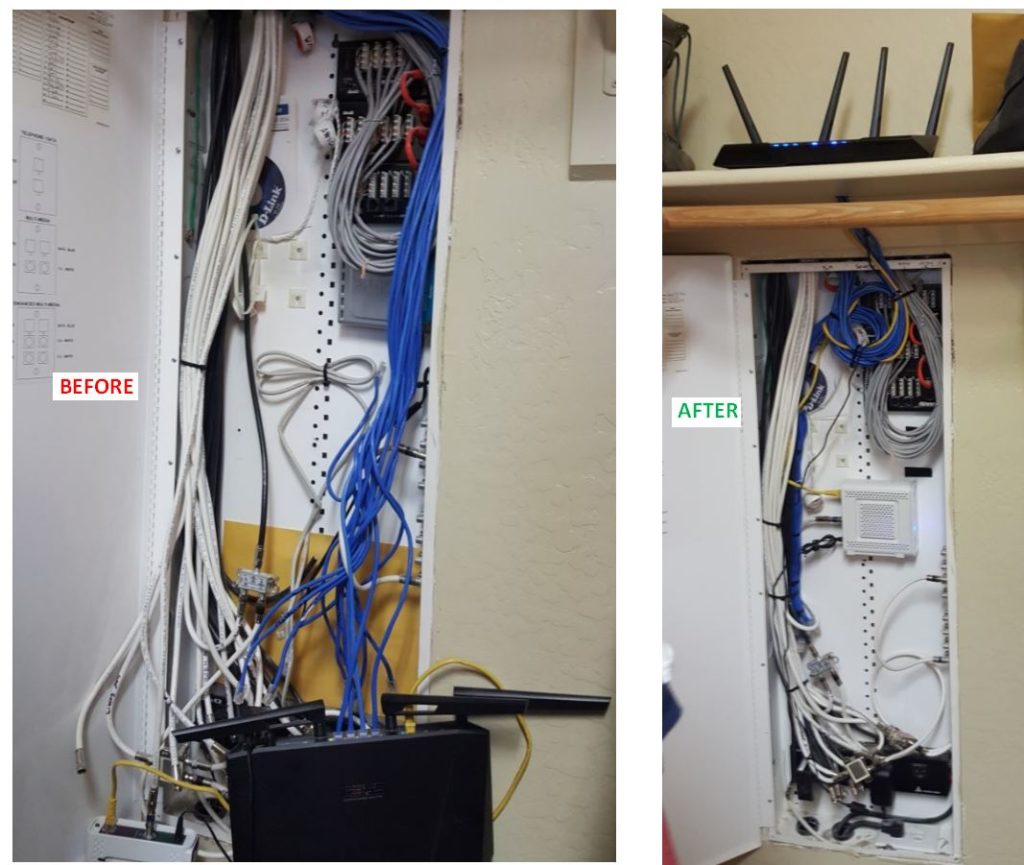
One reason attack hardware is so effective is that it can be difficult to detect. Traditional security controls like firewalls and antivirus software are designed to detect and block software-based attacks, but they can’t protect against physical devices that are plugged into a system.
To protect against attack hardware, it’s important to implement a layered approach to security. This includes measures like restricting physical access to systems, implementing strong access controls, and regularly patching and updating software.
Conclusion:
Attack hardware is a growing threat to computer systems and networks. These physical devices can be used to bypass traditional security controls and gain persistent access to a system. To protect against attack hardware, it’s important to be aware of the threat and to implement a layered approach to security. By taking steps to secure your systems against attack hardware, you can help ensure that your data and systems remain safe from cyber threats.
If you like this article and think it may be helpful to others, please use the social media link(s) below to share it. Also, please feel free to leave your comments below. Thank you ! Paul~